Scam-backscatter
Overview
Scam-backscatter prevents backscatter (accept and bounce) on mail servers which don't host mailboxes locally. It validates mailboxes by verifying the recipient addresses hosted on a different mail server.
Performance
Scam-backscatter was designed to use minimal resources. It can filter several hundreds of thousands SMTP connections or more depending on system and hardware configuration. Our statistics show that the milter stops approximately four in every five messages as the recipient addresses are invalid. That translates into a 80% decrease in mail filtering requirements.
Backscatter mail
Backscatter is when a mail server accepts an email with a forged sender address, then generates a bounce (non-delivery receipt - NDR) to the sending address. The figure below shows an example where the sender address is forged:
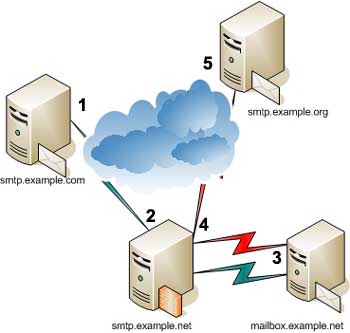
- An email is sent by smtp.example.com with a forged sender address of user1@example.org to user2@example.net.
- The email is accepted for delivery by smtp.example.net.
- The email is then forwarded to mailbox.example.net.
As there is no user2 mailbox on mailbox.example.net, a bounce message (non-delivery receipt) is generated by mailbox.example.net to notify the sender address (user1@example.org) of the delivery failure.
- The bounce message is sent to the mail server at smtp.example.org.
- user1@example.org receives the bounce message.
Your mail server can prevent backscatter by validating the recipient email address in step 2.
Installation
Please read the INSTALL and README files for more information.
Prerequisites
You should have sendmail version 8.12.x or higher installed. Sendmail should
have been built with MILTER support enabled.
You should have the milter library and development kit installed
Build
1. Extract the scam-backscatter tarball
2. Change the current directory to the one where the scam-backscatter source code was extracted.
3. If you are using OpenBSD or NetBSD, rename the Makefile.bsd file
to Makefile. If you are using FreeBSD, rename the Makefile.freebsd file.
If you are using a Linux distribution, rename the Makefile.linux file to Makefile
The Makefile.bsd file can be used for Solaris.
4. Type make and press Enter to compile Scam-backscatter
Additional features
If USEMAILERTABLE is defined as a compile-time switch, Scam-backscatter reads the list of domains to verify and the backend SMTP server IP address from sendmail's mailertable file.
If EHLO is defined, use EHLO instead of HELO when verifying against backend.
When BITBUCKET is defined, Scam-backscatter silently deletes invalid recipients. This feature is not recommended as it can cause loss of mail.
The ALLDOMAINS feature turns on verification of recipient addresses for all domains against the SMTP backend. The BackAddrDomain setting is not required.
Install
1. Copy the scam-back file created above to the appropriate location
(/usr/local/sbin for example)
2. Generate a new sendmail configuration (sendmail.cf) with the following
additional settings:
INPUT_MAIL_FILTER(`scam-back', `S=unix:/var/spool/scam/scam-back.sock, F=T, T=S:240s;R:240s;E:5m')dnl
The line should be added to the .mc file used to create the sendmail.cf.
3. Create a user (scamback for example) which will be used to run the milter
4. Create the /var/spool/scam directory
5. Verify that the user created in step 3 has read-write access to the
/var/spool/scam directory
Alternately, you can use a TCP socket for the milter by using the following for
step 2:
INPUT_MAIL_FILTER(`scam-back', `S=inet:8900@localhost, F=T, T=S:240s;R:240s;E:5m')dnl
Start the milter with the -p inet:8900@localhost parameter.
Using Scam-backscatter
Configuration
The configuration file used is /etc/mail/scam.conf.
Define the domain which you want to protect against backscatter and the IP address of the internal mail server in /etc/mail/scam.conf file as follows:
BackSMTPServer:192.168.0.2
BackAddrDomain:example.net
The BackSMTPServer can be either a hostname or an IP address. The setting should be defined before the BackAddrDomain setting. When there are multiple BackSMTPServer settings, the BackAddrDomain setting is mapped to the BackSMTPServer setting preceeding it.
Only one BackSMTPServer setting is allowed with the ALLDOMAINS feature.
These two settings are not required with the USEMAILERTABLE feature as the mapping of BackAddrDomain to BackSMTPServer is read in from the mailertable file.
The following entry is optional. It should be used if the backend mail server is running on a non-standard port. Scam-backscatter will use tcp port 25 by default.
BackSMTPPort:25
Once Scam-backscatter verification finds a valid email addresses, it gets cached. The default expiry value is 86400 seconds.
BackValidAddrExp:86400
Invalid email addresses are also cached by scam-backscatter. The default expiry value is 3000 seconds.
BackInvalidAddrExp:3000
When BackAddrSubdomain is set to yes, Scam-backscatter will verify subdomain email addresses (user@mail.example.net) as well if example.net is listed as a domain to be verified. This default value is no.
BackAddrSubdomains:Yes
The BackList setting points to the file where the list of valid and invalid recipient addresses is read from at startup and saved to at shutdown.
BackList:/var/spool/scam/backscatter.txt
The TimeoutSMTPconnect setting determines the time to wait (seconds) for a connection to the backend SMTP server.
TimeoutSMTPConnect:2
The TimeoutSMTPReply setting determines the time to wait (seconds) for a reply from the backend SMTP server after sending a SMTP command.
TimeoutSMTPReply:3
Your users can bypass the backscatter verification by relaying through your
server using port 587 instead of port 25.
BackSkipDaemon:MSA
BackSkipDaemon:MSA-v6
If your configuration file has one or more BackSkipDaemon settings, add the MSA daemon as it is only automatically included when the setting is not defined.
BackSkipVerify:127.0.0.1
Recipient validation is skipped for the IP address. This setting also accepts a cidr such as 192.0.2.0/24
BackSkipVerify:192.0.2.2
BackSkipVerify:192.0.2.32/28
Scam-backscatter does not perform verification for locally submitted mail.
BackErrorTempfail:No
By default, Scam-backscatter does not return a temporary failure if the
Backend SMTP server cannot be reached. Setting BackErrorTempfail to
Yes will return a temporary failure.
The Mailertable setting provides the path to the mailertable file. The default value is /etc/mail/mailertable if the setting is undefined.
Mailertable:/etc/mail/mailertable
You can use the following configuration to validate recipient addresses against different backend SMTP servers:
BackSMTPServer:192.0.2.1
BackAddrDomain:example.net
BackSMTPServer:192.0.2.2
BackAddrDomain:example.org
Startup
1. Start scam-backscatter milter as a daemon
scam-back -p unix:/var/spool/scam/scam-back.sock -u scamback -D
2. Restart sendmail if you have generated a new sendmail configuration when
installing scam-backscatter
The -b path parameter specifies the file location where Scam-backscatter
will read the recipient addresses at startup or save them at shutdown.
For example:
scam-back -p unix:/var/spool/scam/scam-back.sock -u scamback \
-b /var/spool/scam/backscatter.txt -D
To display usage and features compiled in, type:
scam-back -h
Shutdown
Type the following command to stop scam-backscatter
kill `cat /var/spool/scam/scam-back.pid`
Multiple backend SMTP servers
You can run multiple instances of Scam-backscatter milter as follows:
First instance:
scam-back -p unix:/var/spool/scam/scam-back.sock -u scamback -D
Second instance:
scam-back -p unix:/var/spool/scam/scam-back2.sock -u scamback \
-f /etc/mail/scam2.conf -P /var/spool/scam/scam-back2.pid -D
Generate a sendmail configuration with the following settings:
INPUT_MAIL_FILTER(`scam-back', `S=unix:/var/spool/scam/scam-back.sock, F=T, T=S:240s;R:240s;E:5m')dnl
INPUT_MAIL_FILTER(`scam-back2', `S=unix:/var/spool/scam/scam-back2.sock, F=T, T=S:240s;R:240s;E:5m')dnl
SMTP Backend out of service
Scam-backscatter can cache valid and invalid recipient addresses. If the SMTP backend is out of service, you can stop the Scam-backscatter milter, increase the BackValidAddrExp and BackInvalidAddrExp values and restart the milter.
Troubleshooting
Scam-backscatter initiates a SMTP session with the Backend SMTP server. If the Backend rate limits SMTP connections, it may cause Scam-backscatter to fail.
Scam-backscatter may fail if it the system runs out of file descriptors.
Refer to your operating system documentation to find out how to increase that.
The following is used on CentOS:
ulimit -n 4096
ulimit -s 2048
You can increase the TimeoutSMTPReply value if the following error messages
appear frequently in your log:
cannot read backend SMTP banner
cannot read helo reply
cannot read mailfrom reply
cannot read rcptto reply
Refer to our milter resource for information about libmilter.
License
Copyright © 2006-2010 Eland Systems All Rights Reserved.
- Redistribution and use in source and binary forms must retain the above copyright
notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright
notice, this list of conditions and the following disclaimer in the
documentation and/or other materials provided with the distribution.
- All advertising materials mentioning features or use of this software
must display the following acknowledgement:
This product includes software developed by Eland Systems
- The name of Eland Systems may not be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Download
The download is provided free of charge subject to our license agreement.
Scam-backscatter source code version 1.5.1 (23 KB)
MD5 63165c21ba6bde4bc0532f4af67c3e09
Previous versions
Scam-backscatter source code version 1.5.0 (22 KB)
MD5 171a95c0d59768df3dae044696bce38a
Scam-backscatter source code version 1.4.3 (22 KB)
MD5 c84619a2cfa7f2e2bab7f45b0c934ac2
Scam-backscatter source code version 1.4.2 (20 KB)
MD5 03c29feff215f28936e72dd8627bfe6d
Scam-backscatter source code version 1.4.1 (20 KB)
MD5 f79a6218b2b2f9550274c62c0885ccf2
Scam-backscatter source code version 1.4.0 (17 KB)
MD5 b81e61868759dff4cced7ae1d1704d1a
Scam-backscatter source code version 1.3.3 (17 KB)
MD5 f9430794ba842d4531da7e5ab75d3b7c
Scam-backscatter source code version 1.3.2 (17 KB)
MD5 cc2088a6c526f5f4fd734be1e29475f5
Scam-backscatter source code version 1.3.1 (19 KB)
MD5 1d9285684a5cb7a38223a3eeb6ed766e
Scam-backscatter source code version 1.3 (19 KB)
MD5 fe354f7f6a0be9dcd0a6c21027837084
Scam-backscatter source code version 1.2.2 (17 KB)
MD5 a62918125125b33365c80b022b084d60
Scam-backscatter source code version 1.2.1 (16 KB)
MD5 929bb8ae82ca3330de332ad6b322c294
Scam-backscatter source code version 1.2 (16 KB)
MD5 922116e2bb034ba161a0ee53be4589fe
Scam-backscatter source code version 1.1 (16 KB)
MD5 4f006dce3beca1f2f89d2cd0f527eb15
Scam-backscatter source code version 1.0 (12 KB)
MD5 c491880120eec9b4066c7e4e8dbaa5c9
Contact
Please send your comments and bug reports to scam+back@elandsys.com.