Firewall
 For
some businesses, security simply means anti-virus software and desktop
firewalls. That leave the end-user in charge of keeping the network
safe with the risks that that entails.
For
some businesses, security simply means anti-virus software and desktop
firewalls. That leave the end-user in charge of keeping the network
safe with the risks that that entails.
Securing the network
Security requires a different mindset and very few have made the leap into the idea of security as a solution. A security solution is not just a firewall or a product; it is a coherent approach to all the possible attacks and loss of information.
The Eland Appliance has been designed with that approach in mind. It enables the enterprise to establish a secure network policy by controlling inbound and outbound connections.
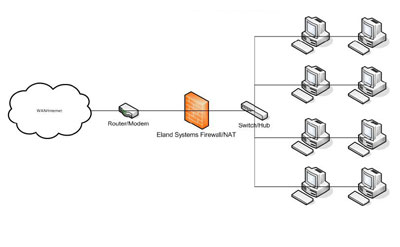
Our default policy blocks incoming traffic. A set of inbound access rules defines which traffic is allowed to enter the network. This means that all traffic not specifically allowed by an access rule is denied.
Stateful Packet Filtering
The key components of a firewall is the packet filter. A packet filter may be stateful; or stateless. The firewall running on the Eland Appliance uses stateful packet filtering to keep track of established connections and makes the decision to allow or reject the packet not only on the contents of single packets but also on the state of the connection.
Protect your network against Attacks
The Eland Appliance can protect your network against attacks such as the SYN attack, Land attack, Tear Drop attack, ICMP/UDP floods, Ping of Death, IP Address Sweep attack, WINNuke attack, ICMP fragment, packets with FIN with no ACK, no flags in TCP, large ICMP packets, packets with SYN and FIN bit set and SYN fragments.
Detect IP Spoofing
IP Spoofing is a technique whereby an intruder sends "messages" to a computer with an IP address indicating that the "message" is coming from a trusted system. In essense, the attacker is fooling the receiving computer into believing that the sender can be trusted. A common misconception is that source IP address can be forged when browsing webpages or sending emails.
IP Spoofing can however be used to generate attacks. The Eland Appliance firewall comes with anti-spoof rules (ingress and egress filtering) to detect and reject packets with spoofed IP addresses. Another attack that can be blocked is source routed packets.
Port scanning
A port is a place where information goes into and out of a computer. Port scanning identifies open ports and can be used to determine which network services are running. Although port scanning has legitimate uses, it can also be used by an attacker to probe for weaknesses before a break-in. The Eland Appliance can be used to block port scans.
Implementing a secure network policy
As part of the installation process, we provide our customers with free advice on how to configure their firewall to implement a secure network policy.